In the past few years there have been a few major newsworthy breaches in American security.
From the Yahoo email hack last year to a breach in our voting system to the multiple lists ISIS have released with names and information of military personnel there are hacks and breaches going on all the time.
Even on the small scale there are issues with personal identity theft daily and yet people are still leaving themselves vulnerable to being scammed without even realizing it. We feel secure when in fact daily we are leaving ourselves open to being the next victim.
A lot of people connected to the military assume that all of these security issues fall under the umbrella of OPSEC.
That is not actually the case.
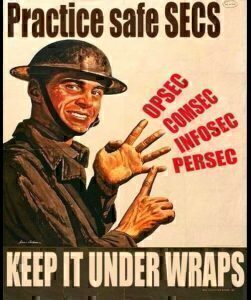
There are four types of security issues and each has its own set of issues and ways to prevent problems from arising. Here is a breakdown of each type of security and what you can do to prevent yourself from falling victim to problems.
OPSEC: Operations Security
To break it down, OPSEC is any information that pertains to mission critical data. Dates, movements, port calls, homecoming, deployments, specific personnel, etc.
And while some people assume it means putting all of that information out together at one time, it really is more than that. It is about letting small pieces slip at a time and then the bad guys are able to piece together enough of it to make a pretty good guess at what is going on and then our military is at risk.
OPSEC is NOT about classified information. It is about the things we don’t really even think about as being risky to talk about.
It’s sitting at a dinner table with your friend telling them about the last port your brother visited on his deployment and answering her questions about what ship he works on.
It is someone seeing a “half my heart is deployed” sticker on your car.
It is blogging about your shopping trip for the upcoming homecoming events, even when you never say what day you will be celebrating.
In the military community OPSEC is a very big deal. It means the difference between troops arriving safely to their next destination or not.
It means the difference between a ship being able to make a port call or having to cancel because a Sailor let it slip to mom on a phone call and mom shared it on Facebook.
Troop movement or activity, operational information, it has to be kept under wraps for a reason.
It is very important that you are aware of your surroundings if you are discussing the deployment of loved ones, a command work-up schedule, or anything else that could fall under the category of OPSEC. You never know who is listening or who is looking at your blog, Facebook, Instagram, or Twitter.
I cannot tell you how many times I have seen an angry commenter ranting away about the news outlets violating OPSEC. They aren’t. They have been given press releases written often times hand in hand with the military public affairs offices. Usually once the news is spouting off about homecoming it is safe for you to talk about it as well. But to be 100% sure you should still contact your commands FRG and verify that you are safe to share. You might feel like you’re being a pest but it is better safe than sorry when it comes to talking about military movement.
PERSEC: Personal Security
To tell the difference between OPSEC and PERSEC just remember that OPSEC has to do more with actions and PERSEC has to deal with people.
PERSEC to a civilian often is linked with the idea of identity theft. It is any personal information about you or your family.
It is amazing the amount of personal information you can find out about a stranger without even asking one question when you start down the rabbit hole of social media.
Even with privacy settings on websites such as Facebook there is still more information available than you would ever believe. And often time people think if they don’t use their name on a blog that no one can tell who they are so they are very open with the details of their life.
Everything from pictures of their children at a school event to discussing buying a new house is shared across social media at a rapid rate because people feel safe when their security is set to private.
It is important to protect your personal information. Most of us are aware enough to not give out our social security number and address to just anyone. Yet, how many times have you applied for a credit card or done online shopping?
===>> You have to put your information onto forms and then cross your fingers that it is used and destroyed in the appropriate manner.
Look at what happened in 2013 at Target. Approximately 40 million credit and debit card accounts as well as data on 70 million customers was breached.
We think we are safe when we are out shopping and yet there are hackers just waiting for a chance to attack. Just do a quick Google search of 2016 data breaches and you can see how often these are happening and how much it is costing people to repair the damage from them.
Now, before you start to panic and decide hiding your cash under the mattress is safer than having anything to do with traditional banking, understand that hiding does not help you. It just scares you and living in fear is no way to live.
Instead just be aware and be alert to things that seem off. Be smart about checking your credit report to make sure that you aren’t the victim of identity theft before it costs you thousands of dollars.
Be careful who you talk to about your personal information. Do maintain high privacy setting on social media but understand that anything you put out there is out there forever. Do not post things you wouldn’t want complete strangers knowing about you if you are not prepared for possible fallout from it. Your safety is more important than being the next viral star.
COMSEC: Communications Security & INFOSEC: Information Security
I want to touch quickly on COMSEC and INFOSEC because they are not securities we think about often.
COMSEC deals with protecting communication as it is transmitted. Emails, phone calls, and good old fashion snail mail all fall under COMSEC.
Unless you are working around classified information, it is unlikely you will have to worry about how you are talking to people. But please be aware that unless you are working from a secure server or a secure phone line there is always a small risk of your messages being hacked into. Hackers and COMSEC go hand in hand and often these breaches in security lead to INFOSEC issues.
INFOSEC deals with the information being transmitted. To use a lighthearted example, if your spouse is deployed and you decide it’s a good idea to keep a bit of spice in the marriage so you email off a raunchy email and then hear from your spouse that they were informed by the command IT guy that the email was intercepted you are dealing with COMSEC and INFOSEC.
Your transmission wasn’t private and then the information in the email wasn’t private. Again, this is something you are not as likely to have to worry about if you aren’t working in a high security job, but do keep it in mind when you are placing orders online or talking to the bank on the phone. Make sure you read the websites privacy policy when it comes to personal data and ask bank reps if they are calling from secure lines.
They should know that and if they do not, ask to talk to someone who does know the policies.
I know talking about security isn’t fun. I know people think that they are doing enough to protect their families from any possible breaches in security. And I know some people read these type of articles and it leads them into a tailspin of feeling scared and worrying about every little move they make.
That is not what I want to happen to you.
I just want you to be aware of your surroundings, be aware of the possibility of breaches and be aware that there are ways to fix problems should something outside of your control happen to shake your foundation. Because no matter how many steps you take to protect yourself there is always a risk of problems arising but being prepared and “Practicing Safe SECS” will certainly minimize the possibility that you will be the next victim we read about in the news.